- Solutions
- AgenciesSolutions for:
- Employee BenefitsBackEmployee Benefits
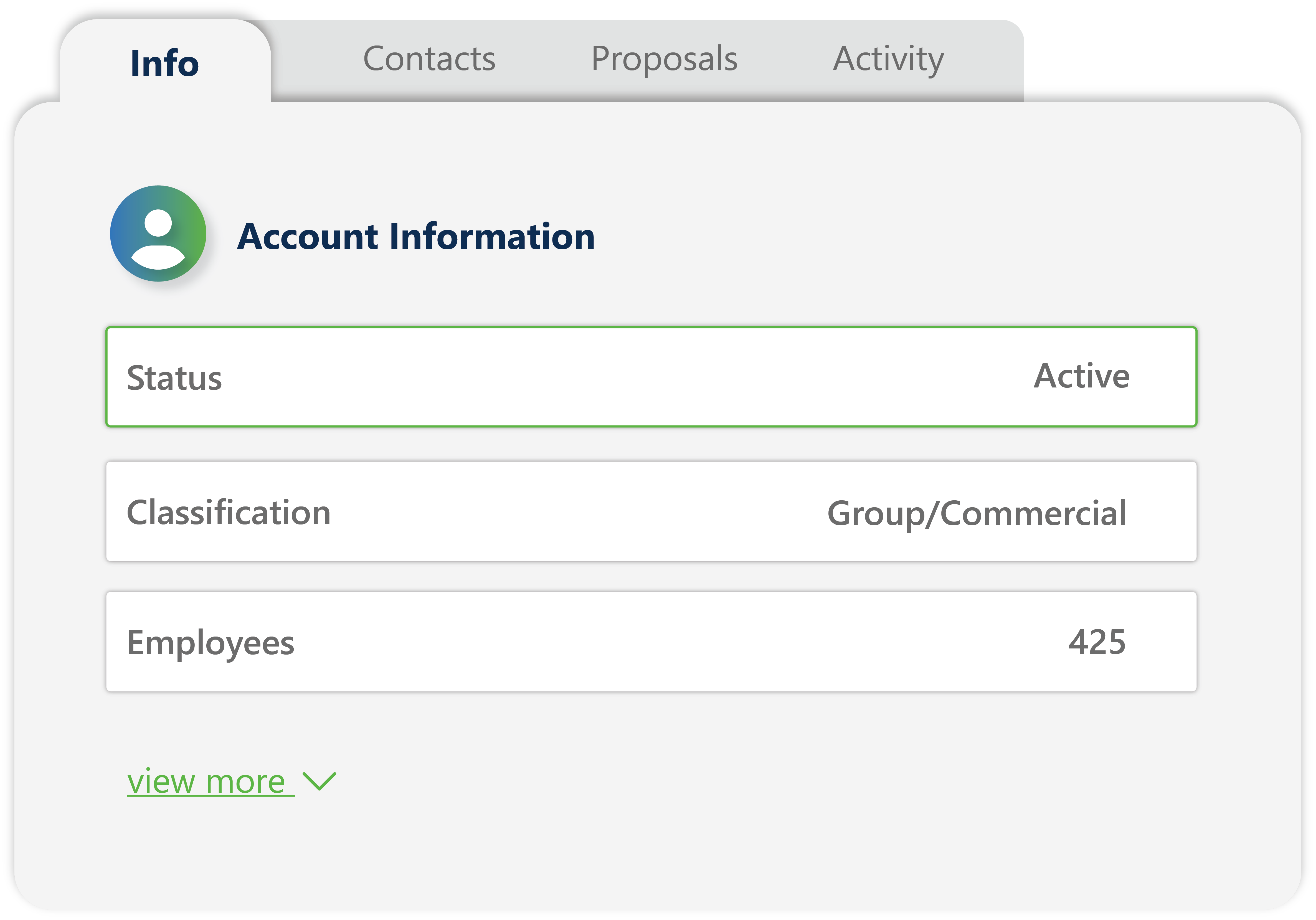
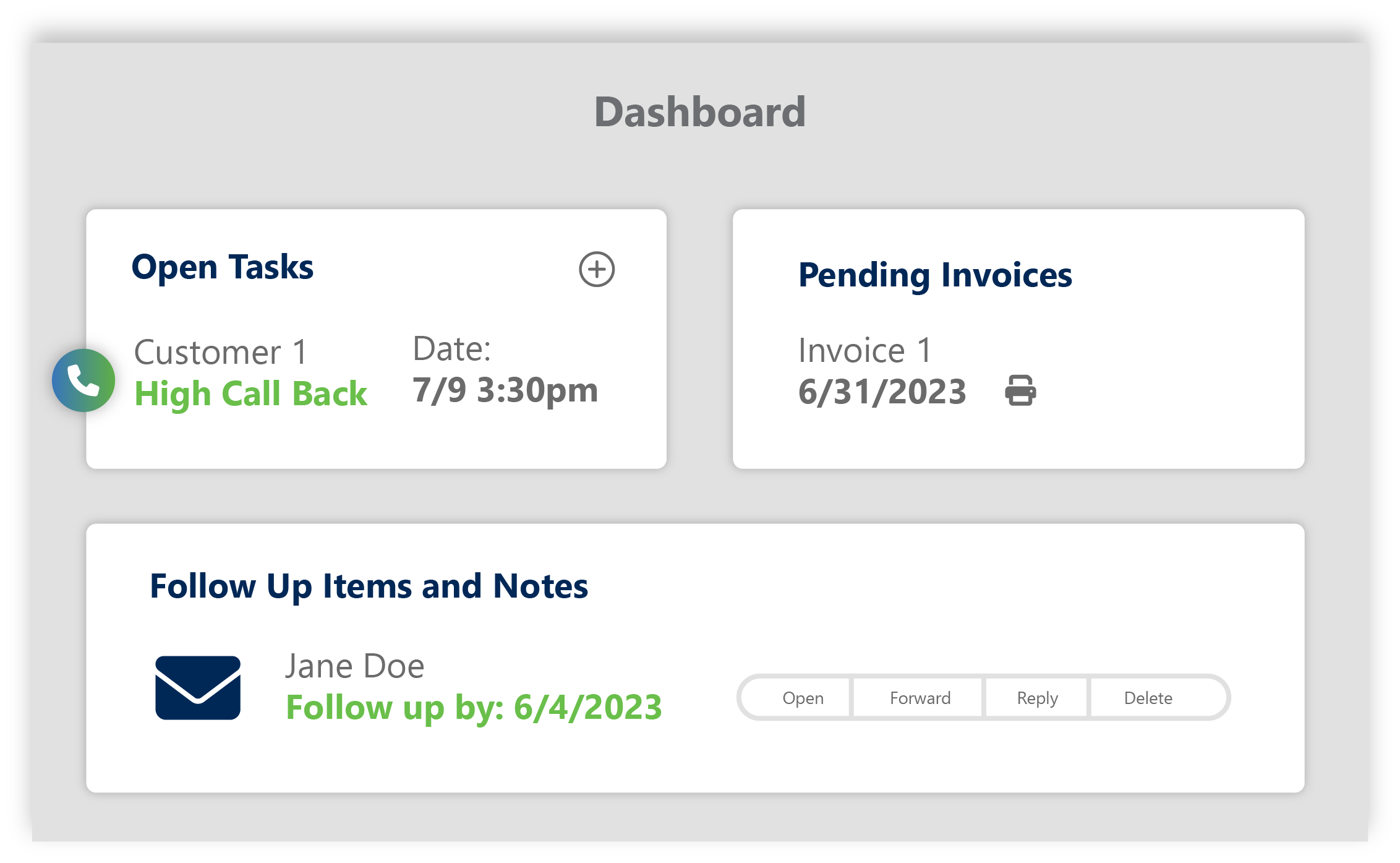
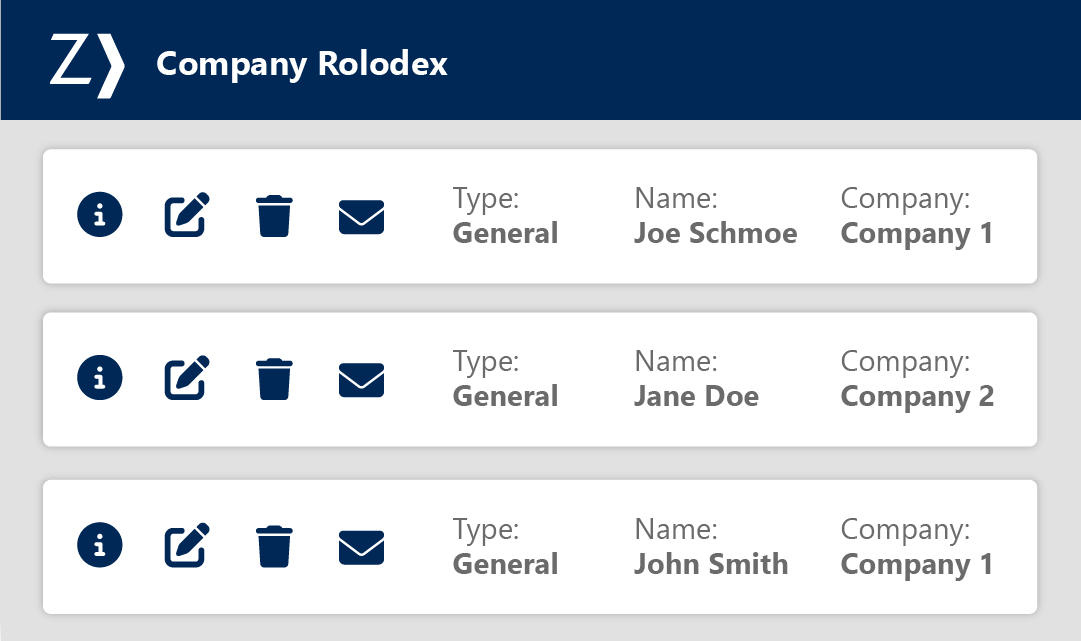
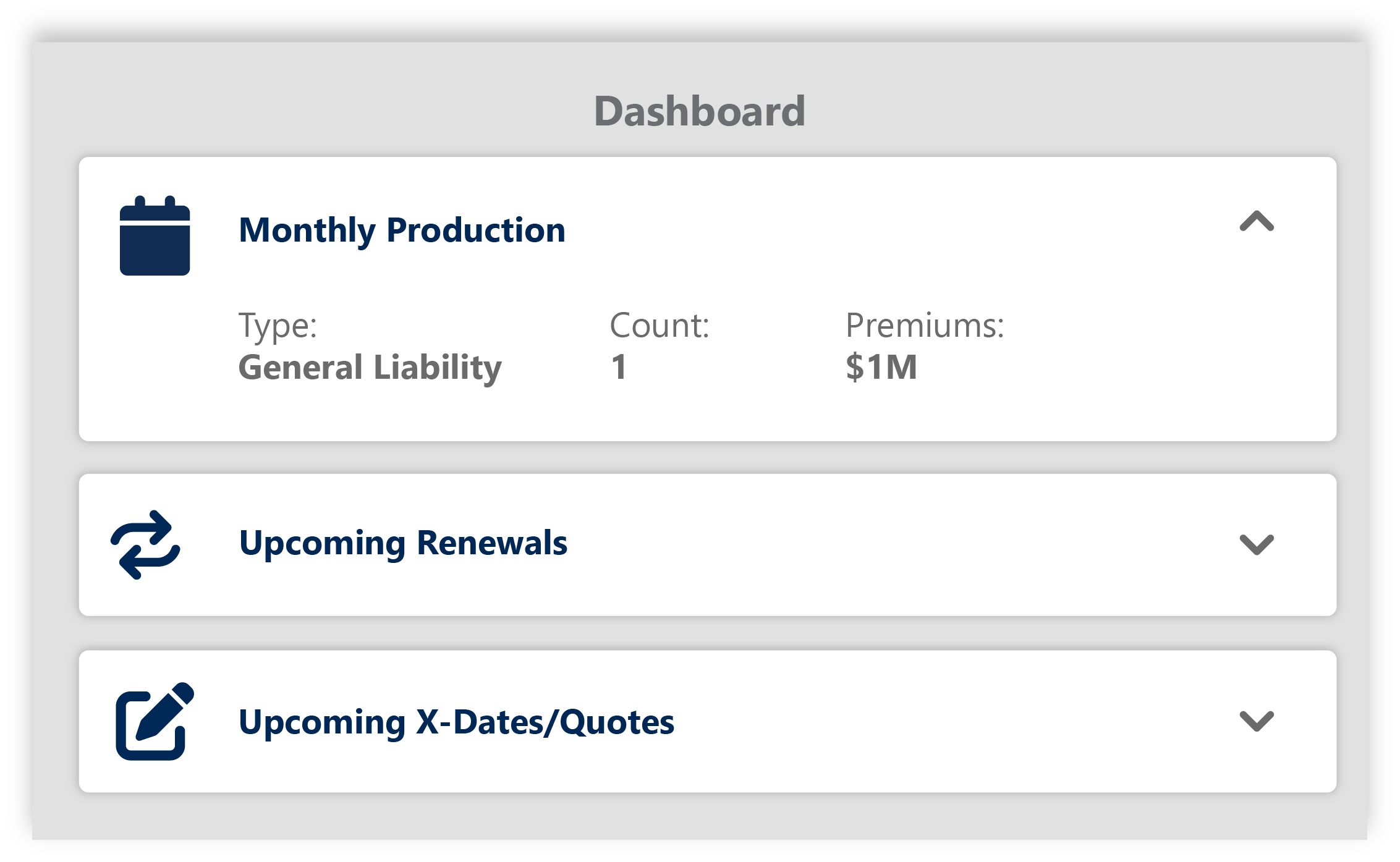
- Sales CloudStreamline mission-critical benefits workflows - from prospecting to renewals - fueling organic growth for your agency.
- Client CloudBetter serve your clients & your bottom line by providing added tools and resources.
- Content CloudHarness the power of employee benefits content to drive growth through engagement and education.
- Analytics CloudDeliver confidence with medical plan analysis.
Featured StoryAs part of their integrated technology solutions, Decisely is leveraging carrier-direct data via the Group Benefits API to enhance their quoting processes. Learn more >

- Commercial LinesBackCommercial Lines
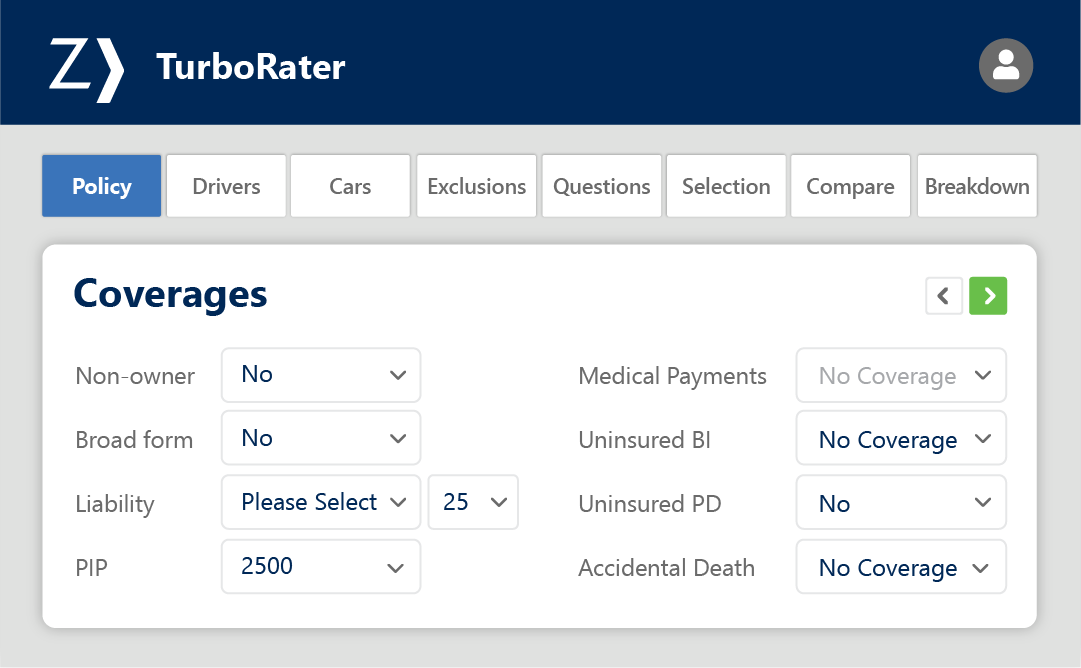
- Sales CloudStreamline mission-critical P&C workflows - from prospecting to renewals - fueling organic growth for your agency.
- Client CloudHelp clients self-serve, manage their people through compliance, risk management and safety solutions.
- Content CloudHarness the power of P&C content to drive help manage risk and drive engagement.
- Analytics CloudClaims and loss analysis made easy to drive value.
Featured StoryCyber losses are on the rise, and cyber insurance is in high demand. Now with Cyber Quoting, quoting cyber insurance has never been simpler. Discover how it works

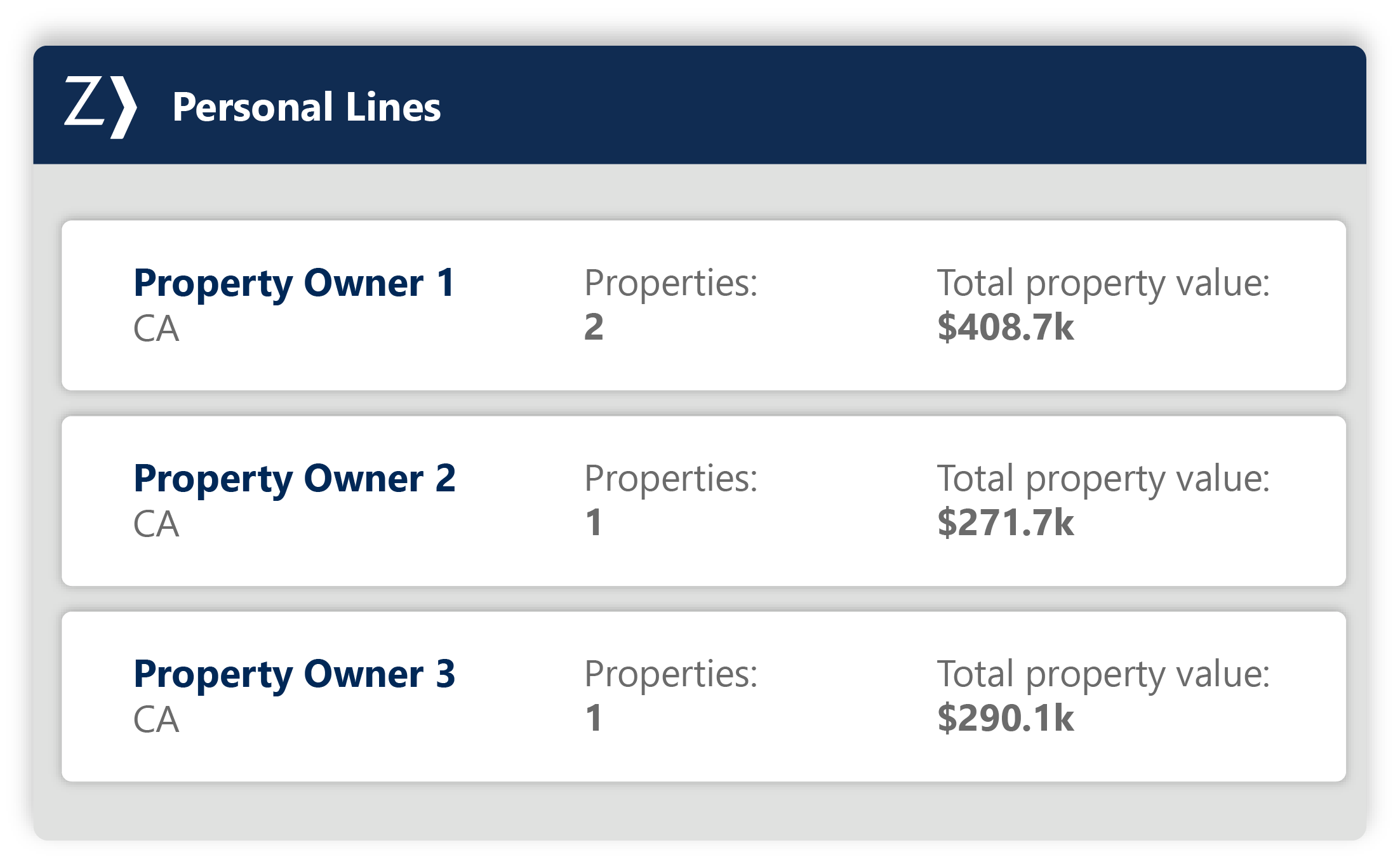
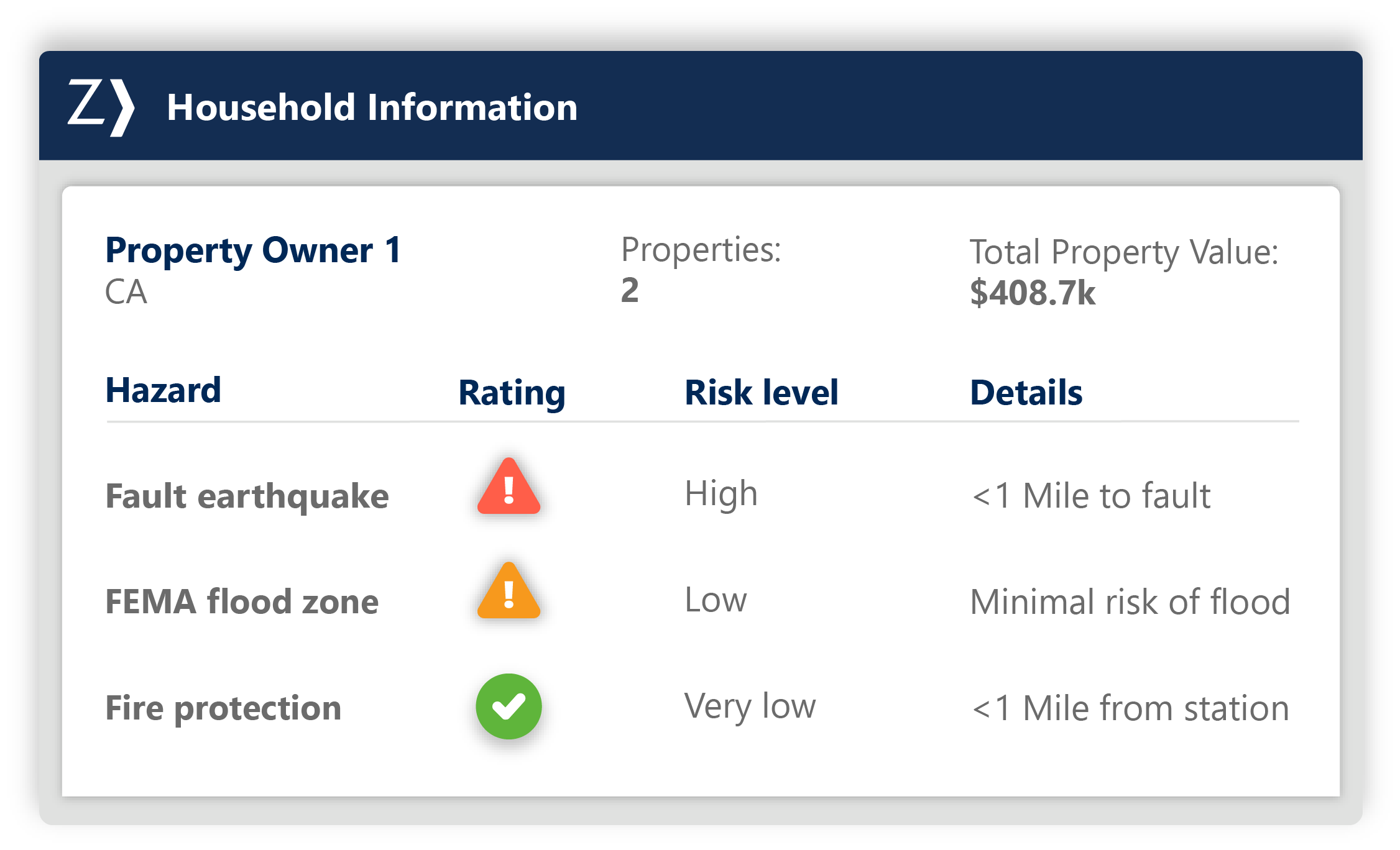
- Personal Lines
- Employee Benefits
- InsurersBackInsurersFeatured Story
Zywave’s Digital Distribution Suite – ClarionDoor has been recognized as a Luminary in the Celent Report for Insurer Stand-Alone Rating Engines – Global Edition. This report outlines the key elements that insurers need to consider when choosing a stand-alone rating engine.
Read more > - Service ProvidersFeatured Story

Learn how Redwood Credit Union used the Personal Lines Quoting API to drive cross-sell opportunities within their organization.
Read the story >
- Agencies
- Training & Support
- Events
- Resources
- About ZywaveBackAbout Zywave